To update, download and run the new installer.
To update, download the new app and replace the old one.
If you installed TurboWarp Desktop from an app store or package manager, download the update from there. Otherwise, manually reinstall the app the same way you installed it.
To update, reinstall the app the same way you installed it.
or
Download installer for Windows 10+ (64-bit)Free code signing provided by SignPath.io, certificate by SignPath Foundation.
If a Windows SmartScreen alert appears, click "More info" then "Run anyways".
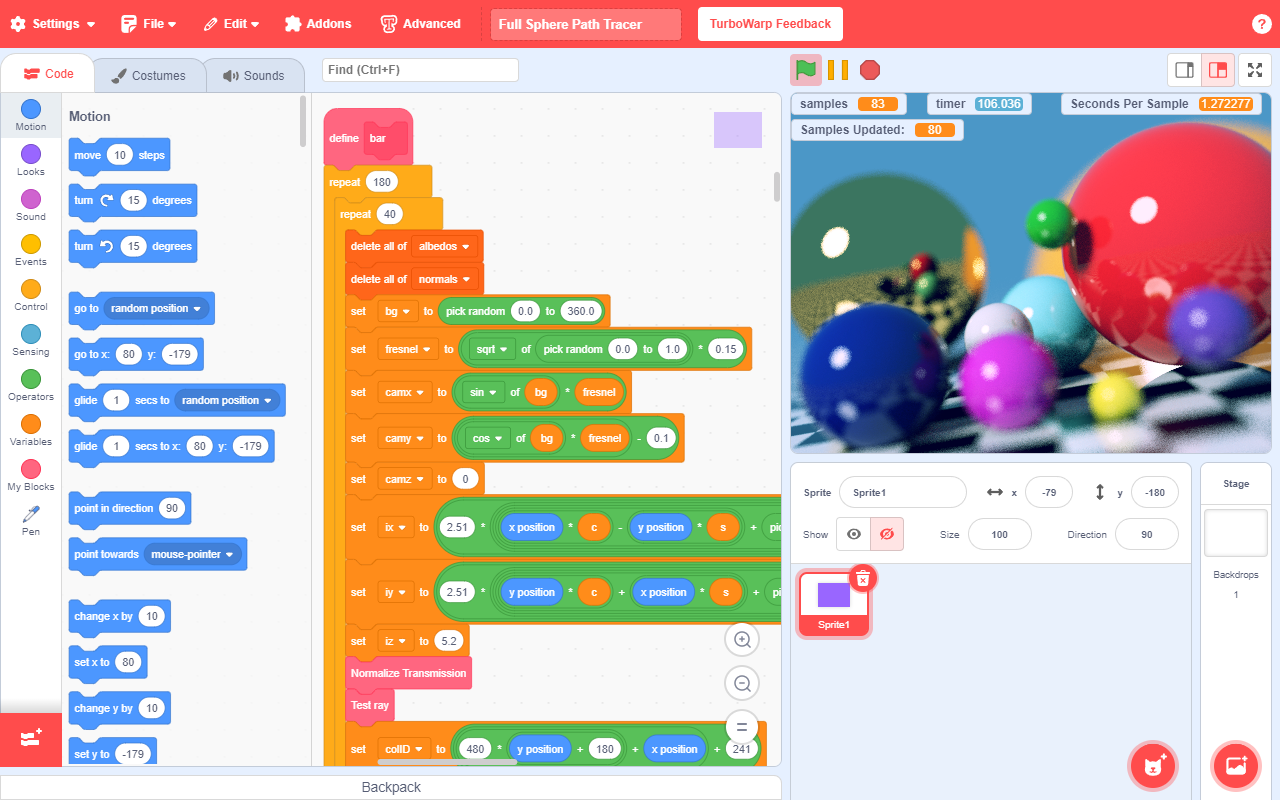
By compiling projects to JavaScript, they run 10-100x faster than in Scratch.
Uses significantly less memory and idle CPU usage than Scratch.
Your eyes will thank you.
Replace Scratch's default 30 FPS with any framerate of your choosing or use interpolation.
Built in packager to convert projects to HTML files, zip files, or applications for Windows, macOS, or Linux.
Change Scratch's default 480x360 stage to any size you like.
Includes new extensions such as gamepad and stretch, and supports loading custom extensions.
Remove almost any of Scratch's arbitrary limits, including the 300 clone limit.
Put scripts, costumes, sounds, or entire sprites into the backpack to re-use them later.
Searchable dropdowns, find bar, jump to block definition, folders, block switching, and more.
Full support for transparency, an improved costume editor, onion skinning, and more.
Enable the cat blocks addon to get cute cat blocks any day of the year.
Analysis of the ssh-20-cisco-125 Vulnerability: A Critical Examination of SSH Weaknesses in Cisco Devices
The ssh-20-cisco-125 vulnerability is a critical security weakness in the SSH protocol implementation on certain Cisco devices. This vulnerability can allow unauthorized access to sensitive network devices, potentially leading to a complete compromise of the device. Network administrators and cybersecurity professionals must prioritize patching vulnerable devices, implementing access controls, and monitoring device logs to mitigate this vulnerability.
Thanks!
The SSH protocol is a widely used secure protocol for remote access to network devices. It provides a secure channel for data transmission, authentication, and management of network devices. However, like any complex software, SSH implementations can be vulnerable to security weaknesses.
Arjun
The ssh-20-cisco-125 vulnerability refers to a critical security weakness in the Secure Shell (SSH) protocol implementation on certain Cisco devices. This vulnerability has significant implications for network administrators and cybersecurity professionals, as it can allow unauthorized access to sensitive network devices. In this paper, we will examine the nature of the ssh-20-cisco-125 vulnerability, its impact on Cisco devices, and provide recommendations for mitigation and remediation.
Cheers
Have a great day!
Exploiting the ssh-20-cisco-125 vulnerability requires an attacker to send a specially crafted SSH packet to a vulnerable Cisco device. The packet must be designed to trigger a buffer overflow condition, which can allow the attacker to execute arbitrary code on the device.
The ssh-20-cisco-125 vulnerability is caused by a weakness in the way Cisco devices handle SSH connections. Specifically, the vulnerability occurs when an attacker sends a specially crafted SSH packet to a Cisco device, which can cause a buffer overflow condition. This buffer overflow can allow an attacker to execute arbitrary code on the device, potentially leading to a complete compromise of the device.
Get it from the Microsoft Store to enable automatic updates.
Or download an installer.
TurboWarp Desktop uses a free code signing provided by SignPath.io, certificate by SignPath Foundation.
These versions of the app have the same features but are slower and less secure. Support will be removed at an unknown time in the future. If a Windows SmartScreen alert appears, click "More info" then "Run anyways".
Install from the Mac App Store for automatic updates.
Or download the app manually. Open the .DMG, then drag TurboWarp into Applications. If it tells you that TurboWarp already exists, choose "Replace".
Download for macOS 12 and laterThese versions of the app have the same features but are slower and less secure. Support will be removed at an unknown time in the future. Open the .DMG, then drag TurboWarp into Applications. If it tells you that TurboWarp already exists, choose "Replace".
Analysis of the ssh-20-cisco-125 Vulnerability: A Critical Examination of SSH Weaknesses in Cisco Devices
The ssh-20-cisco-125 vulnerability is a critical security weakness in the SSH protocol implementation on certain Cisco devices. This vulnerability can allow unauthorized access to sensitive network devices, potentially leading to a complete compromise of the device. Network administrators and cybersecurity professionals must prioritize patching vulnerable devices, implementing access controls, and monitoring device logs to mitigate this vulnerability.
Thanks!
The SSH protocol is a widely used secure protocol for remote access to network devices. It provides a secure channel for data transmission, authentication, and management of network devices. However, like any complex software, SSH implementations can be vulnerable to security weaknesses.
Arjun
The ssh-20-cisco-125 vulnerability refers to a critical security weakness in the Secure Shell (SSH) protocol implementation on certain Cisco devices. This vulnerability has significant implications for network administrators and cybersecurity professionals, as it can allow unauthorized access to sensitive network devices. In this paper, we will examine the nature of the ssh-20-cisco-125 vulnerability, its impact on Cisco devices, and provide recommendations for mitigation and remediation.
Cheers
Have a great day!
Exploiting the ssh-20-cisco-125 vulnerability requires an attacker to send a specially crafted SSH packet to a vulnerable Cisco device. The packet must be designed to trigger a buffer overflow condition, which can allow the attacker to execute arbitrary code on the device. ssh20cisco125 vulnerability
The ssh-20-cisco-125 vulnerability is caused by a weakness in the way Cisco devices handle SSH connections. Specifically, the vulnerability occurs when an attacker sends a specially crafted SSH packet to a Cisco device, which can cause a buffer overflow condition. This buffer overflow can allow an attacker to execute arbitrary code on the device, potentially leading to a complete compromise of the device.